|
Knoxville residents have plenty of reliable ISPs. These are the best plans, according to CNET's broadband experts.
|
|
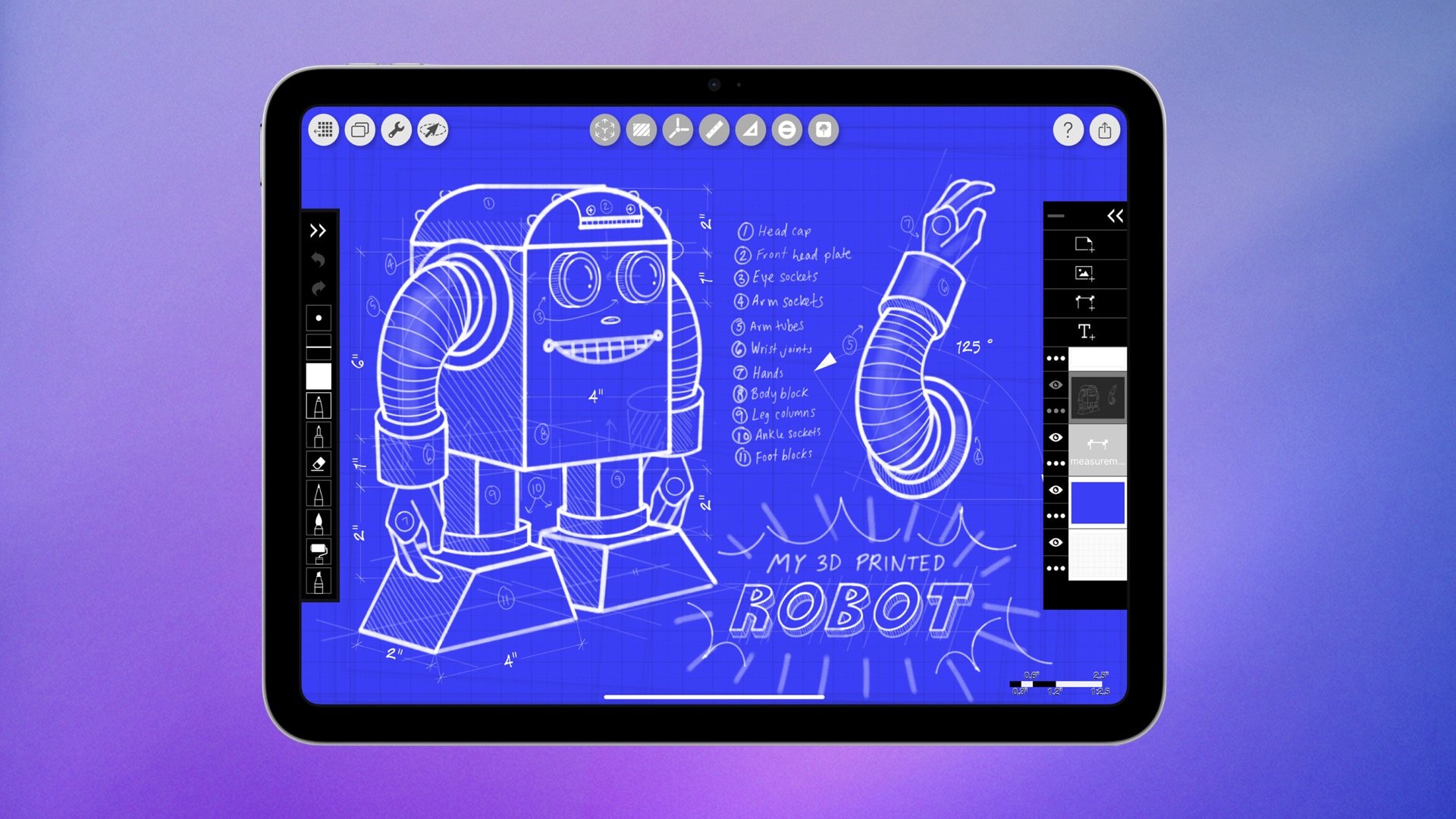 Amazon today is taking up to $65 off Wi-Fi and cellular models of Apple's 11th generation iPad. Prices start at $299.00 for the 128GB Wi-Fi iPad, down from $349.00, a second-best price on this model. Amazon today is taking up to $65 off Wi-Fi and cellular models of Apple's 11th generation iPad. Prices start at $299.00 for the 128GB Wi-Fi iPad, down from $349.00, a second-best price on this model.
|
|
Microsoft is cutting more than 9,000 jobs -- 4% of its global workforce -- and as a result, Everwild and the Perfect Dark reboot have been put out to pasture.
|
|
Plus-size sleepers need support -- but not at the expense of comfort. These are the best mattresses for heavier bodies, tested by CNET's sleep experts.
|
|
Looker by Google and Microsoft Power BI are both business intelligence (BI) and data analytics platforms that each maintain a strong following. These platforms have grown their customer bases by staying current with the latest trends in the data analytics space, ensuring their platforms can handle the digital transformation, data mining, and various big data […]
The post Looker vs. Power BI: 2024 Software Comparison appeared first on eWEEK.
|
|
A UK research team based at Durham University has identified an exploit that could allow attackers to figure out what you type on your MacBook Pro — based on the sound each keyboard tap makes.
These kinds of attacks aren't particularly new. The researchers found research dating back to the 1950s into using acoustics to identify what people write. They also note that the first paper detailing use of such an attack surface was written for the US National Security Agency (NSA) in 1972, prompting speculation such attacks may already be in place.
"(The) governmental origin of AS- CAs creates speculation that such an attack may already be possible on modern devices, but remains classified," the researchers wrote.
To read this article in full, please click here
|
|
